Posted on January 17, 2022 at 4:45 PM
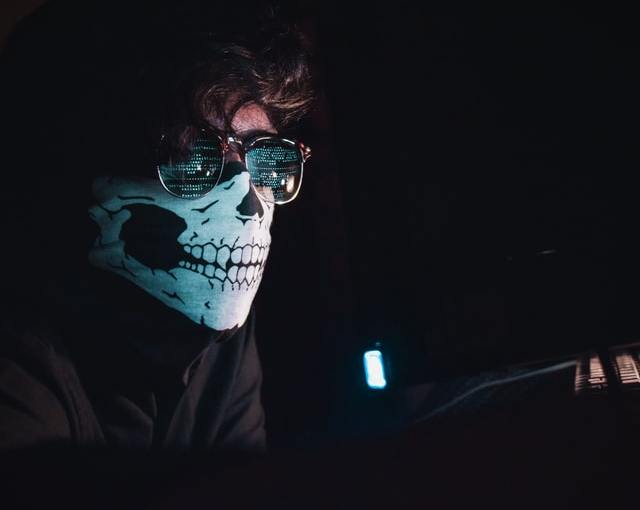
Hackers threaten to delete stolen data by demanding ransom in cryptocurrencies
Over the past year, incidences of cybersecurity attacks have hit the roof. Threat actors have been changing their attack tactics to evade detection and ensure they can infiltrate the servers of even the largest organizations.
The latest victim of these attacks is one of India’s leading private finance companies. Threat actors infiltrated this company and gained access to their servers. In most cases, such hackers demand ransom by threatening to leak sensitive data. However, in this case, the hackers demanded ransom by threatening to delete critical data.
Hackers demand payment in crypto
The incident happened last week where an executive from the victim company filed a complaint with the Airport Police. According to the complaint, the company had received a threatening email from a hacker stating that the company’s important data would be deleted if demand were not met.
The complaint noted that the hacker had demanded to be paid 11.63 crore worth of cryptocurrencies not to carry out the threat. The cyber police noted that this was a new trend used by hackers to extort companies.
The agency noted that the incidences of hackers bullying companies into paying for their information to be spared were on the rise. The hackers threatened individuals and companies that their data would be erased if they failed to pay the ransom. Additionally, the hackers usually state that they have control over the company’s servers, which allows them to alter the stored data.
Additionally, the hackers demand to be paid the ransom in cryptocurrencies. This allows them to escape detection. The use of cryptocurrencies has become highly popular among cybercriminals taking advantage of the anonymous nature of crypto transactions to conduct attacks for financial gains.
The senior police inspector at Cyber Police, DS Hake, noted that “the extortion, if collected, is not done physically. The sender has to transfer the cryptocurrencies from one e-wallet to another e-wallet. It is an easy delivery, easy acceptance, and less risky.”
Similar cases have been reported
As aforementioned, these cases have been on the rise, and the Cyber Police has registered three similar cases within the past 12 months. In all of these cases, the hackers demanded to be paid in cryptocurrencies, making it harder for the authorities to trace the transactions.
Hake noted that one of the catalysts attributed to the rise in these attacks is the work from home model. With companies delegating tasks to individuals in different locations, sensitive information has been left vulnerable, which the hackers are taking advantage of.
“Many techies are working from home, and they are using laptops and desktops. The techies are using their own internet networks to do the office work. In such a scenario, the suspects hack the laptops or desktops of the individuals using ransomware and unsecured network connections or by sending emails to the victims.”
The Cyber Police note that in two of the reported cases, the hackers gained total control over the laptops of the victims. The hackers then contacted the individual demanding to be paid in the form of cryptocurrencies to relinquish their control over the laptop.
“None of the techies or the company paid the ransom, and they approached the police with their complaints,” Hake added. The police also added that an individual or a company was given a specific timeframe within which they had to pay the ransom. Those that failed to pay within the given time ended up receiving a higher ransom demand, which in most cases, was double the amount asked for originally.
The police further noted that if the company or individual failed to pay the ransom, the hackers fulfilled their threat by deleting the files. Additionally, the malware used by the hackers to conduct this attack was sophisticated such that it spreads rapidly in the company’s servers. The malware also evolved quickly, which prevented cybersecurity experts from launching mitigations that will help stop the malware.
Hake added that “cyber extortionists compress important files/data stored on the server or computer using the encryption software and then they demand ransom to decrypt or decode. The companies or individuals must not open the suspicious emails having encrypted messages stored in them.”
Hake concluded by asking companies to be wary of these attacks because they can be “hard to crack.” The responsible individuals or companies had to take the necessary precautions to ensure their data was preserved. The nature of these attacks becomes even more complex due to the use of cryptocurrencies for payments, which fails to reveal the hackers’ identities.